Spam campaign impersonating us targets T-Online users in Germany | Infinium-tech
Have you received an email advertising a cybersecurity subscription or smart ring that appears to come from GSMArena.com? We didn’t send that email – it came from a spam service pretending to be us.
Several T-online.de users reached out to us to report spam emails, which prompted us to address the issue. To be clear, we have nothing to do with the email or cyber security thing they advertise. Some spam emails look like this:
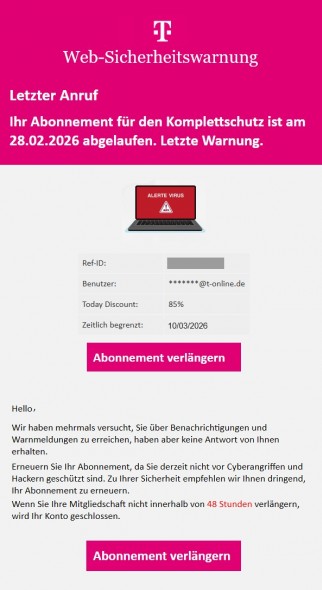
This is what some spam emails look like
If you have received a spam email like the one seen above, you should contact your email provider’s support team and let them know about the problem.
Spammers are copying our email addresses – this means they are falsely setting GSMArena.com as the email sender. In particular, the email looks like it comes from tpjdlgcj@gsmarena.com, but it is not an active account on our servers (the random jumble of letters is apparently generated at random). Instead the emails are coming from a Microsoft owned server (52.103.140.27) and an Oracle owned server (92.5.13.127), neither of which are part of our infrastructure. These are probably cloud hosts used by spammers.
This is an old trick and your email provider should have blocked these emails. We have contacted the provider to clarify the situation and it is taking steps to improve its spam filtering. We’re also doing our part to make spoofing harder in the future.
There are established tools in place to fight domain spoofing that spammers are using. Without getting into too many technical details, a reverse dns check It will turn out that the sender’s IP address does not match the GSMArena.com IP address, which is a major threat signal. additional equipment such as spf, DKIM And DMARC Similarly it can identify spam emails that use spoofing. For our part, we’ve set our SPF policy to “hardfail”, which will tell email providers to block emails that don’t originate from our servers.












Leave a Reply